Benchmarking attacks on standardized LWE parameters
Apparaît dans la collection : 2024 - T3 - WS1 - Deployment of post-quantum cryptography
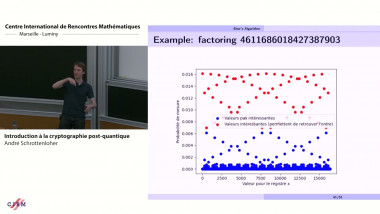
Lattice cryptography schemes based on the learning with errors (LWE) hardness assumption have been standardized by NIST for use as post-quantum cryptosystems, and by HomomorphicEncryption.org for performing encrypted computations on sensitive data. Thus, understanding their concrete security is critical. Most work on LWE security focuses on theoretical estimates of attack performance, which is important but may overlook attack nuances arising in real-world implementations. Existing concrete benchmarking efforts such as the Darmstadt Lattice Challenge do not include benchmarks relevant to the standardized LWE parameter choices—such as small secret and small error distributions, and Ring-LWE (RLWE) and Module-LWE (MLWE) variants. To improve our understanding of concrete LWE security, we provide the first benchmarks for LWE secret recovery on standardized parameters, for small and low-weight (sparse) secrets.
We evaluate four LWE attacks in these settings to serve as a baseline: the Search-LWE attacks uSVP [9], SALSA [ 51], and Cool&Cruel [44], and the Decision-LWE attack: Dual Hybrid Meet-in-the-Middle (MitM) [22]. We extend the SALSA and Cool&Cruel attacks in significant ways, and implement and scale up MitM attacks for the first time. For example, we recover hamming weight 9 − 11 binomial secrets for KYBER (κ = 2) parameters in 28 − 36 hours with SALSA and Cool&Cruel, while we find that MitM can solve Decision-LWE instances for hamming weights up to 4 in under an hour for Kyber parameters, while uSVP attacks do not recover any secrets after running for more than 1100 hours. We also compare concrete performance against theoretical estimates. Finally, we open source the code to enable future research.